⭐PRs or any form of contribution will be appreciated⭐
Read in other Languages: 🇬🇧English, 🇰🇷한국어, 🇨🇳简体中文, 🇷🇺Русский, 🇯🇵日本語
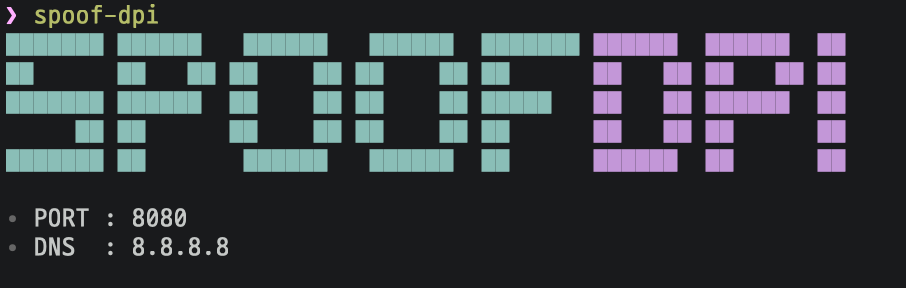
A simple and fast software designed to bypass Deep Packet Inspection
SpoofDPI will be installed in ~/.spoof-dpi/bin.
To run SpoofDPI in any directory, add the line below to your ~/.bashrc || ~/.zshrc || ...
export PATH=$PATH:~/.spoof-dpi/bin
# macOS Intel
curl -fsSL https://raw.githubusercontent.com/xvzc/SpoofDPI/main/install.sh | bash -s darwin-amd64
# macOS Apple Silicon
curl -fsSL https://raw.githubusercontent.com/xvzc/SpoofDPI/main/install.sh | bash -s darwin-arm64
# linux-amd64
curl -fsSL https://raw.githubusercontent.com/xvzc/SpoofDPI/main/install.sh | bash -s linux-amd64
# linux-arm
curl -fsSL https://raw.githubusercontent.com/xvzc/SpoofDPI/main/install.sh | bash -s linux-arm
# linux-arm64
curl -fsSL https://raw.githubusercontent.com/xvzc/SpoofDPI/main/install.sh | bash -s linux-arm64
# linux-mips
curl -fsSL https://raw.githubusercontent.com/xvzc/SpoofDPI/main/install.sh | bash -s linux-mips
# linux-mipsle
curl -fsSL https://raw.githubusercontent.com/xvzc/SpoofDPI/main/install.sh | bash -s linux-mipsleYou can also install SpoofDPI with go install
$ go install github.com/xvzc/SpoofDPI/cmd/spoof-dpi@latestYou can also build your own
$ git clone https://github.com/xvzc/SpoofDPI.git
$ cd SpoofDPI
$ go build ./cmd/...Usage: spoof-dpi [options...]
-addr string
listen address (default "127.0.0.1")
-debug
enable debug output
-dns-addr string
dns address (default "8.8.8.8")
-dns-port int
port number for dns (default 53)
-enable-doh
enable 'dns-over-https'
-no-banner
disable banner
-pattern value
bypass DPI only on packets matching this regex pattern; can be given multiple times
-port int
port (default 8080)
-system-proxy
enable system-wide proxy (default true)
-timeout int
timeout in milliseconds; no timeout when not given
-v print spoof-dpi's version; this may contain some other relevant information
-window-size int
chunk size, in number of bytes, for fragmented client hello,
try lower values if the default value doesn't bypass the DPI;
when not given, the client hello packet will be sent in two parts:
fragmentation for the first data packet and the rest
If you are using any vpn extensions such as Hotspot Shield in Chrome browser, go to Settings > Extensions, and disable them.
Run spoof-dpi and it will automatically set your proxy
Run spoof-dpi and open your favorite browser with proxy option
google-chrome --proxy-server="http://127.0.0.1:8080"Since most of websites in the world now support HTTPS, SpoofDPI doesn't bypass Deep Packet Inspections for HTTP requets, However It still serves proxy connection for all HTTP requests.
Although TLS encrypts every handshake process, the domain names are still shown as plaintext in the Client hello packet. In other words, when someone else looks on the packet, they can easily guess where the packet is headed to. The domain name can offer a significant information while DPI is being processed, and we can actually see that the connection is blocked right after sending Client hello packet. I had tried some ways to bypass this, and found out that it seemed like only the first chunk gets inspected when we send the Client hello packet splited in chunks. What SpoofDPI does to bypass this is to send the first 1 byte of a request to the server, and then send the rest.
Green Tunnel by @SadeghHayeri GoodbyeDPI by @ValdikSS